6
.
8.
. #! ' (
A A A
%AAA& "
"
!" #" +
6 0 7. #" #!
#!
" . 144
! #!
! #
%!#& ' (
.
B 99 #! ' ( A
.
.
<
.
!#
0 - !#
. !# ' (
#
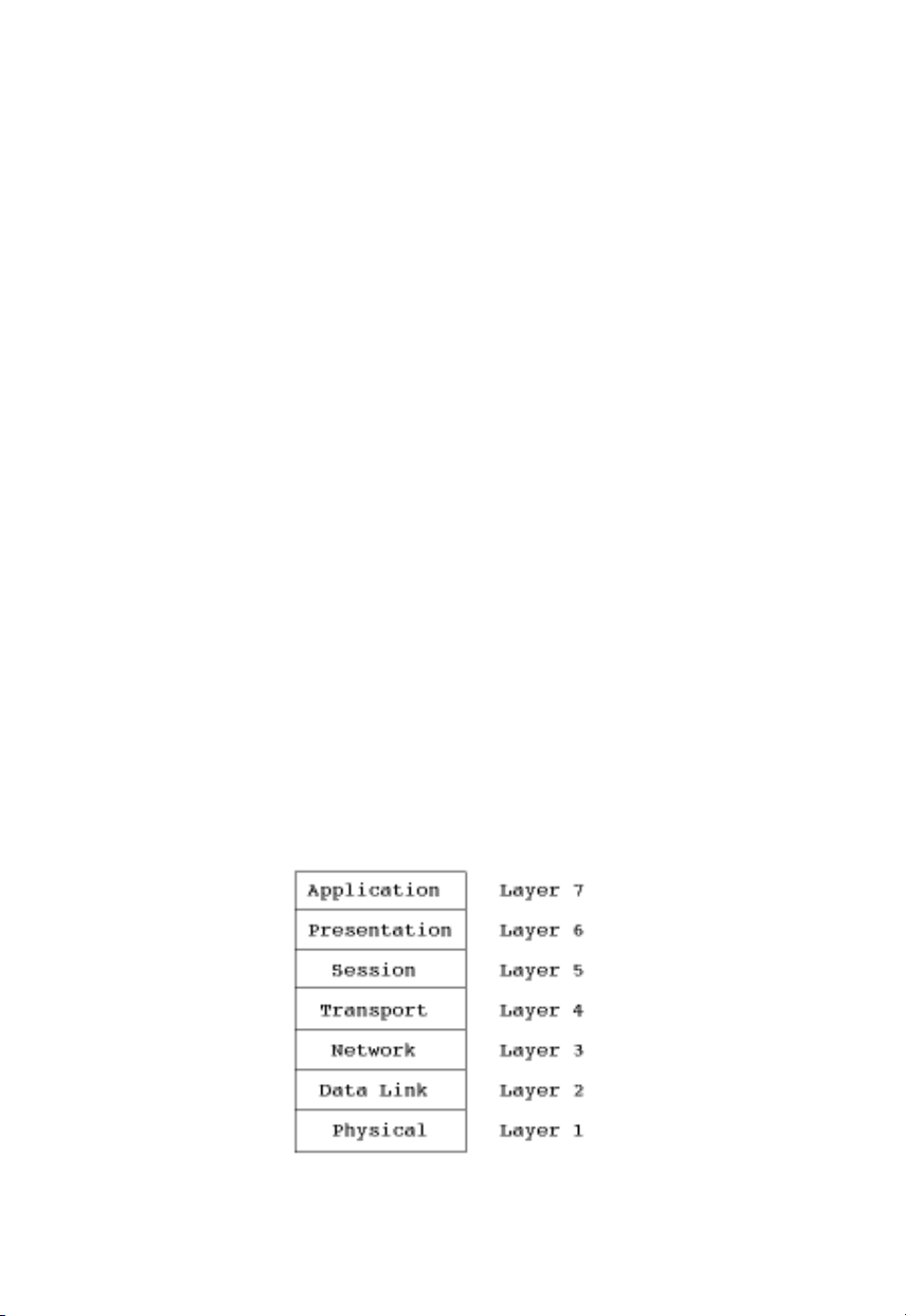
! The International Organization for Standardization (ISO) Open System
Interconnection (OSI) Reference Model

.
AAA.
$%! &' ( '!)* "&+,
) 1 5. #! ' (
< 1. .
.
. 5
)
. n
n1
#!$ ' ( .
Layer 1: the physical layer
- .
. .
.
Layer 2: the data link layer
.
.
.
. 9
-
- .
" .
.
.
!
-
. A. '. B,,
" -

/ !#
. 0
+ AAA >49 .
D < < %<<& ( -
%(-& <<
. (-
.
<
Layer 3: the network layer
#! ' ( -
.
#
. . .
. 0. .
.
0
.
# ?
E9@ .
. 6$ A
%E&. %&
Layer 4: the transport layer
#!$ ' (
.
A . 0 .
.
.
-
. #.
. 0
.
.

.
-
.
.
A
6$ #0 A %#E&
%& + , %+,&
. .
+, .
Layer 5: the session layer
!# ' (
. .
.
Layer 6: the presentation layer
#!$ !# ' (
. .
!
.
.
!
Layer 7: the application layer
!# ' (
A
. .
"

) ' ( .
.
. .
- .
B %B&. . 8
%8& @ 5
$($ /&0
- #!
.
n n1 #!
B 9?
#! ' ( #
.
$%! 1+2&)
* .
A A A %AAA& AAA
<-6 +#-.
- 6 # %-6#&
+# .
, <-6 . AAA "
< < %<<& ( -
%(-& (- .
.
<-6 A (-
A$ # ( - , %#(-,&
'$ 0 - (-
. <-6. << << .
AAA .
. .
Addressing
- AAA (- B
AAA D
A 3
%'!(&

![Biến Tần FR-A700: Sổ Tay Hướng Dẫn Cơ Bản [Chi Tiết]](https://cdn.tailieu.vn/images/document/thumbnail/2019/20191130/cac1994/135x160/1741575103503.jpg)
![Xử lý số tín hiệu: Tài liệu thí nghiệm [Chuẩn SEO]](https://cdn.tailieu.vn/images/document/thumbnail/2018/20180821/danhvi27/135x160/7141534836177.jpg)






![Catalogue Insulators: [Thêm từ mô tả phù hợp với nội dung catalogue]](https://cdn.tailieu.vn/images/document/thumbnail/2015/20150608/sincos/135x160/6521433725774.jpg)






![Bài giảng công tắc tơ [mới nhất]](https://cdn.tailieu.vn/images/document/thumbnail/2026/20260506/vispacex_27/135x160/93891778142285.jpg)
![Giáo trình Điện tử tương tự 1: Phần 1 [Mới nhất]](https://cdn.tailieu.vn/images/document/thumbnail/2026/20260506/vispacex_27/135x160/69111778210056.jpg)








